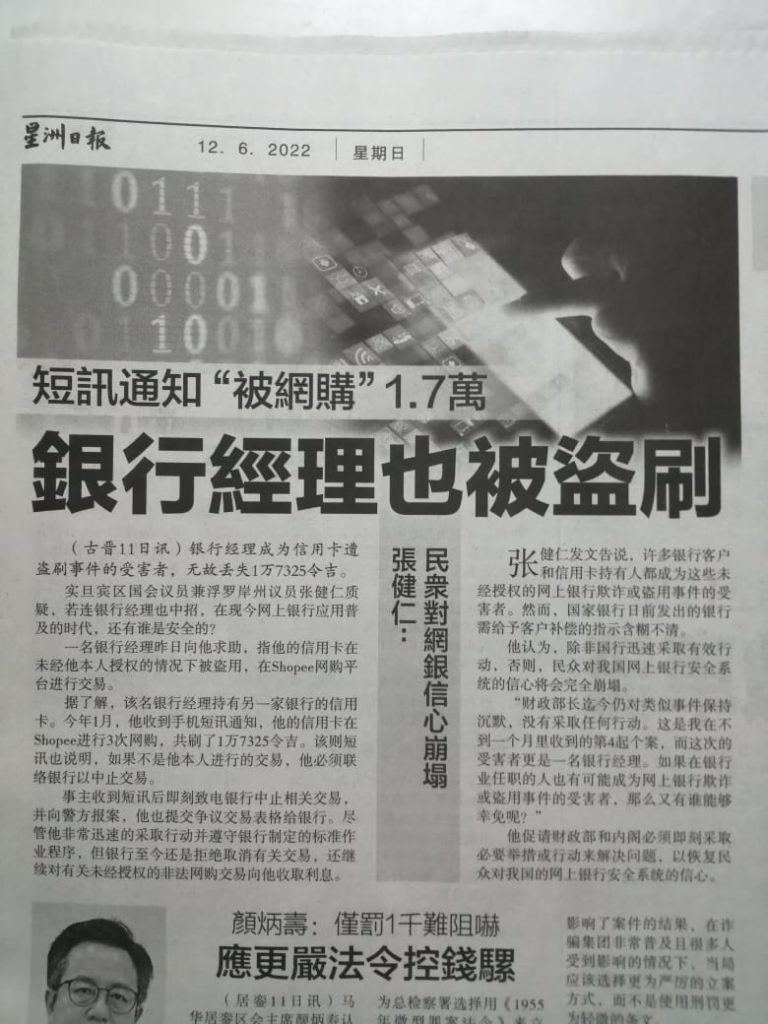
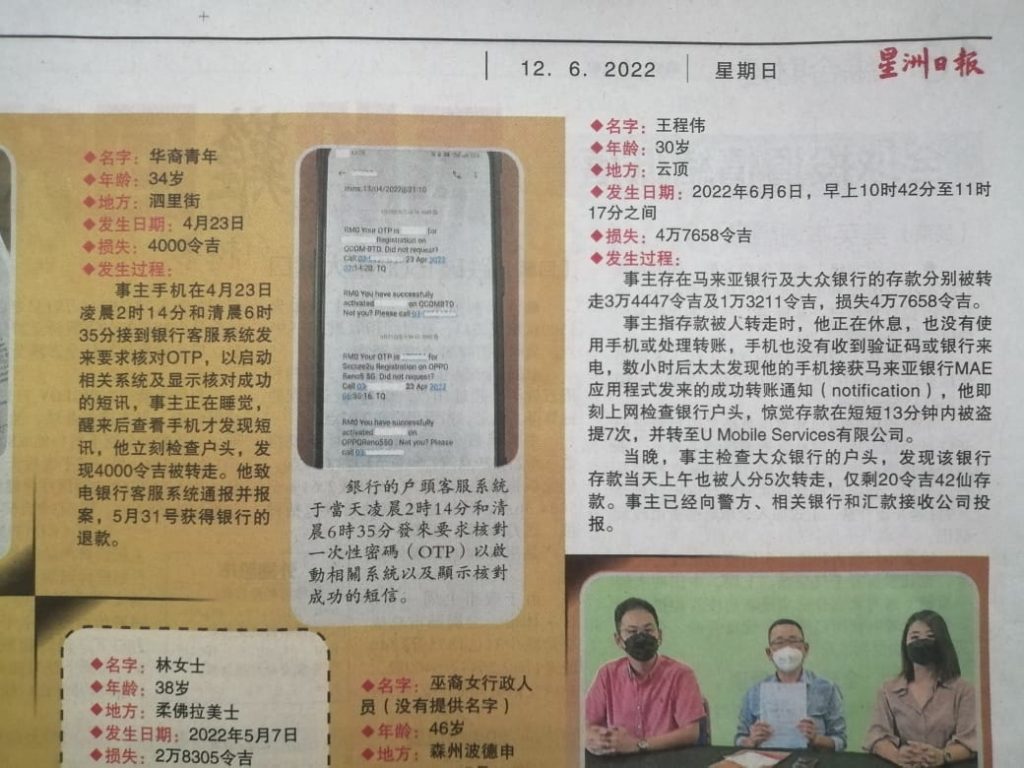
Recently, news about hackers wired out money from banks without OTPs and without owners realization splashed across newspapers. Such news raise questions about the security of online shopping and banking system. As a result, people — especially those who are IT-illiterate– started to question about the safety of online transactions, and many might just shy away from it all together.

But truth to be told, such attacks rarely target the back-end banking system; instead they rely on sophisticated social engineering to trick users– yes, that’s YOU, the one I am talking at, right now– into divulging your account secrets. In other words, there are things you can do to prevent or at least minimize the chances of being tricked.
There are blog and Facebook posts written on how to protect yourself against such attacks, ranging from don’t side-load apps to don’t give apps SMS permissions to ensure that the login image is familiar to pay attention to the banking URLs. All are very correct, the authors are very well-learned, and the tips given are absolutely fantastic. You will sound wiser if you can regurgitate what they say and of course, your bank account will be safe too.
But here I want to give you a simple rule that always works, a rule that you can easily remember and tell your grandchildren even though you have no foggiest idea about what I am going to talk about. Memorizing without understanding is superstition, but this rule will allow you to be superstitious and safe, at the same time.
But before you get to that, I want to give you a crash course about OTP/TAC– one time password/transaction activation code, and how it came about.
The original use case of OTP is that when you perform the transaction on a computer, you then need to use a second device– your phone– to receive another transaction code. The idea is that the hackers can compromise your computer, or they can compromise your phone, but it’s highly unlikely that they can compromise both at the same time, and then being able to connect the two and establishing them as one entity. So as long as you use two devices, the difficulties in scamming increase many times over, and make it an unprofitable vector of attack. An unprofitable vector of attack is also less worked on, which renders it even less potent.
Also back in the good old days, your phone was likely a dumb phone whereby you can only send and receive SMSes. No Mobile Legends, no Banking apps, no Facebook/Instagram/tiktok on the device and certainly not the kind of addictive device it now is. So the chances of hackers penetrating your dumb phone is even less ( unless you are a terrorist wanted by Mossad) .
In other words, what really kept the transaction activity secured was not so much the One Time Password that we are now familiar with, but rather the Two Factor Authentication–– you need to authenticate yourself twice on different physical media.
But then, time changes. IPhone started the Smart Phone revolution, and more and more online activities are being carried out on a 5 inch computer that we happen to call ‘Smart Phone’. And gradually, we forgot the Security lesson 101 that we learnt in a hard way; we thought that it was the OTP kept us secure, but in fact, it was the Two Factor Authentication that did the job.
So what happens now is that you initiate a banking transaction on your phone, and then you receive the OTP on the same device. All the hackers need to do, is to just compromise you on this one device, and then they can have a field day. Of course they still have to trick you a number of times successfully, but it’s way easier to do that on a device rather than on multiple ones.
So here’s the cardinal rule: just forget about what I said ( if you so wish), and
Always ensure that you authenticate yourself twice on two, physically separated device. And then never give away your OTP
OK, so what does that have to do with eReader?
Here’s a good news for eReader fans, hackers will never able to successfully carry out such an attack if you are using eReaders rather than your phones to buy or read books.

The reason is simple, eReaders don’t come with SMS apps, so there is no way for hackers to read and send SMSes on your behalf surreptitiously. However compromised your eReaders are, the hackers can’t steal your money like how they can if you are on your phone.
Secondly, Boox supports Google Play Store, always, if you got it from booxmalaysia.com ( If you got it from elsewhere and you find that it’s not available, you may contact us and see where it leads us). The Google Play Store apps are vetted, and so unlike the apps you side-loaded, they do go through some form of security review before being released. This reduces the chances of you downloading phishing apps greatly. Let’s hope that the rising heat of geopolitics won’t change this fact!